Surveillance strategies in the UK and Israel often go global
the feds are so pissed they can’t break encryption, which is essentially just math, are they gonna ban math?
Isn’t like building a basic encryption tool coding 101? I didn’t build one when I was learning to code, but I did have to make a caesar cipher scrambler/unscrambler with python years ago. I don’t have the code or remember how to do it, but does that make me a hostile actor now?
These people are clueless
they are evil, not necessarily clueless.
What is the fundamental difference. Evil men and arrogant idiots might as well be the same thing.
focusing on the ‘they are idiots’ fallacy completely misdirects blame and disencourages deeper critical thought. they have a plan and we need one too.
the real misdirection is focusing on individuals and their blame. The real question is why does UK political system produces these people rule and how do they keep ruling.
Both parties were captured by the aristocracy/super rich, call them what you will, and they support a total surveillance of a population they obviously fear and want tools to persecute as they see fit. Starmer is a perfect example of this, he’s done more damage arguably than the tories did in over a decade. Their betrayal of the country will throw the elections to the far right too, that is the only protest vote against the status quo, and they will affix themselves in power and implement even worse privacy.
A popular reform party would fix the problems but the aristocracy is too greedy and arrogant for that, thinking they can control a far right party or otherwise shut them out electorally indefinitely and continue to sell out the public to the rich, even as discontent is increasing and the plutocratic rot is visible on the surface and spread throughout the whole.
sure, focusing on how dumb they are isn’t very condusive to discussing the intricacies of capitalism.
seriously though, they do have a plan. we need to figure out ours.
Ironically that’s kinda the argument being made in the document above
They don’t care how it affects normal people’s lives or what we sacrifice to pay for their incompetent leadership.
It doesn’t affect just normal people, but when you make encryption weaker, the foreign state (i.e. bad actor) surveillance also benefits.
It denies normal people the ability to retain their privacy from corporate and government surveillance.
Which is exactly what any government these days wants.
“Never attribute to stupidity that which is adequately explained by malice.”
or something like that…
Our governments are hostile. Act accordingly.
deleted by creator
All of them, AFAIK
No way this lasts or holds up to basic scrutiny. End to end encryption is a de-facto standard for so fucking much technology.
Like fucking HTTPS.
Well if they commit to this, it will never affect “e2ee” options that collaborate with feds e.g. whatsapp, imessage. If you can kill Refaat Alareer with it rest assured you will be able to keep it in your phone anytime
Yes, the trick is to outlaw it entirely then enforce the law selectively against those whom you find politically awkward.
TLS is not typically considered end-to-end encryption. It’s transport encryption.
Fuck this shit. The UK is not longer a free country. And fuck Israel even more for their damned work over the decades to make this possible.
it never has been a free country
Now that I think about it you are right.
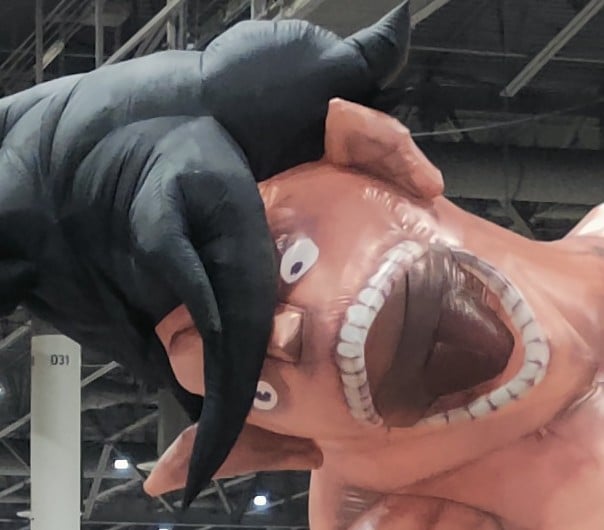
“Innocence proves nothing”
Some 40k shit.
Does it say that explicitly in the document? I know that’s the overall message they’re getting at, but actually typing that out in the doc is darkly funny.
It’s just a fancy, rosy version of just saying “innocence proves nothing”.
Seems appropriate, since the game was invented by brits and the Imperium is an unholy amalgamation of the Roman and British Empires
So literally everyone in the UK using any website that uses TLS is now a hostile actor?
Essentially everyone’s a criminal which is a huge boon for the government. They can now get rid of anyone they want at any time, legally.
That’s what the governments in 1984 could do as well.
That is longstanding, the US and the UK both have been writing laws broadly enough for them to take down anyone for them, or at least charge, we all just trust it won’t be abused, but as we’ve seen with the uk and their bad faith terror designations, that trust is misplaced, and the mask is coming off society. They aren’t pretending anymore, and cynically think “democracy” such as it is, is already dead in all but name, it’s only the citizenry that doesn’t know it yet, and or is contesting it.
TLS is not typically considered end-to-end encryption. It’s transport encryption.
I don’t get it. E2ee is about encryption in transit not encryption at rest. TLS sounds exactly like e2ee
E2E is about the sender encrypting, and only the intended receiver decrypting, with nothing in the middle able to read the data.
TLS is not designed for that, as the server you connect to is not necessarily the intended receiver, yet it can see everything.
With E2E, you can send data to a server, which is not the intended receiver, and it won’t be able to read it.
Your explanation assumes that scope and scale are part of the definition which it is not.
If you keep zooming in or zooming out the definition of E2E keeps changing under your statement.
If the only knowledge a system has is between a sender and a receiver (Which satisfies even your definition of “intended recipient”) then TLS is E2E encrypted.
The definition of E2EE has evolved since the concept surfaced. You seem to be stuck with the original meaning.
TLS does not fit the modern definition.
Yes the technical term has evolved but did the term evolve in the legislation definition of it?
If not, then the technically correct usage doesn’t matter which is a point I’ve made in another comment as well.
And in my previous comment, I am pointing out the logical inconsistencies. Not that I agree or disagree with the technical terminology. You seem to be conflating a logical explanation/call-out of logic holes for my opinion, which it is not
Removed by mod
Do they strictly define end to end encryption in this bill?
If not, then yes, TLS is “end to end” as the sender encrypts the message, and the receiver decrypts it. Each “end” to each “end” is encrypted, satisfying the semantics of the term.
Paving roads makes it easier for an invading army to get around.
No-one’s invading Lincolnshire then.
Easier, not possible.
This is great.
If you are (or know) a UK citizen, please let them send this with the above context to their representative.
What I see here is that the UK is a hostile entity towards humanity. So, fuck the UK government and all their parties. Since we’re here, fuck the French government as well, just in case.
Makes me want more E2E encryption.
A Cypherpunk’s Manifesto
By Eric Hughes
Privacy is necessary for an open society in the electronic age. Privacy is not secrecy. A private matter is something one doesn’t want the whole world to know, but a secret matter is something one doesn’t want anybody to know. Privacy is the power to selectively reveal oneself to the world.
If two parties have some sort of dealings, then each has a memory of their interaction. Each party can speak about their own memory of this; how could anyone prevent it? One could pass laws against it, but the freedom of speech, even more than privacy, is fundamental to an open society; we seek not to restrict any speech at all. If many parties speak together in the same forum, each can speak to all the others and aggregate together knowledge about individuals and other parties. The power of electronic communications has enabled such group speech, and it will not go away merely because we might want it to.
Since we desire privacy, we must ensure that each party to a transaction have knowledge only of that which is directly necessary for that transaction. Since any information can be spoken of, we must ensure that we reveal as little as possible. In most cases personal identity is not salient. When I purchase a magazine at a store and hand cash to the clerk, there is no need to know who I am. When I ask my electronic mail provider to send and receive messages, my provider need not know to whom I am speaking or what I am saying or what others are saying to me; my provider only need know how to get the message there and how much I owe them in fees. When my identity is revealed by the underlying mechanism of the transaction, I have no privacy. I cannot here selectively reveal myself; I must always reveal myself.
Therefore, privacy in an open society requires anonymous transaction systems. Until now, cash has been the primary such system. An anonymous transaction system is not a secret transaction system. An anonymous system empowers individuals to reveal their identity when desired and only when desired; this is the essence of privacy.
Privacy in an open society also requires cryptography. If I say something, I want it heard only by those for whom I intend it. If the content of my speech is available to the world, I have no privacy. To encrypt is to indicate the desire for privacy, and to encrypt with weak cryptography is to indicate not too much desire for privacy. Furthermore, to reveal one’s identity with assurance when the default is anonymity requires the cryptographic signature.
We cannot expect governments, corporations, or other large, faceless organizations to grant us privacy out of their beneficence. It is to their advantage to speak of us, and we should expect that they will speak. To try to prevent their speech is to fight against the realities of information. Information does not just want to be free, it longs to be free. Information expands to fill the available storage space. Information is Rumor’s younger, stronger cousin; Information is fleeter of foot, has more eyes, knows more, and understands less than Rumor.
We must defend our own privacy if we expect to have any. We must come together and create systems which allow anonymous transactions to take place. People have been defending their own privacy for centuries with whispers, darkness, envelopes, closed doors, secret handshakes, and couriers. The technologies of the past did not allow for strong privacy, but electronic technologies do.
We the Cypherpunks are dedicated to building anonymous systems. We are defending our privacy with cryptography, with anonymous mail forwarding systems, with digital signatures, and with electronic money.
Cypherpunks write code. We know that someone has to write software to defend privacy, and since we can’t get privacy unless we all do, we’re going to write it. We publish our code so that our fellow Cypherpunks may practice and play with it. Our code is free for all to use, worldwide. We don’t much care if you don’t approve of the software we write. We know that software can’t be destroyed and that a widely dispersed system can’t be shut down.
Cypherpunks deplore regulations on cryptography, for encryption is fundamentally a private act. The act of encryption, in fact, removes information from the public realm. Even laws against cryptography reach only so far as a nation’s border and the arm of its violence. Cryptography will ineluctably spread over the whole globe, and with it the anonymous transactions systems that it makes possible.
For privacy to be widespread it must be part of a social contract. People must come and together deploy these systems for the common good. Privacy only extends so far as the cooperation of one’s fellows in society. We the Cypherpunks seek your questions and your concerns and hope we may engage you so that we do not deceive ourselves. We will not, however, be moved out of our course because some may disagree with our goals.
The Cypherpunks are actively engaged in making the networks safer for privacy. Let us proceed together apace.
Onward.
Eric Hughes
9 March 1993
This was written in 1993? Huh, I keep seeing cyber punks around in different contexts too, like some music mixes from some cyber punk festival at least.
In the old days, the British Empire steamed open everyone’s mail and read it, at least coming from the colonies like India.
This is cypherpunk, not cyberpunk. Common roots, but important distinction.
Cyberpunk is an aesthetic style.
Cypherpunk is not.
Cyberpunk is a genre first and foremost. A critique of capitalism set in a corporate dystopia with transhumanist themes.
A lot of the aesthetic is rooted in the culture of the time period that it was created in (the 80s). The cultural fear, more specifically. A time where American corporations, and by extension the US government and population, were afraid of the Japanese economic boom and saw a future where the dollar was replaced by the yen and Japanese supplanted English as the lingua franca of the world, Japanese culture was exported the way American culture is, and Americans started eating their meals with chopsticks instead of forks.
So google, amazon and Microsoft are hostile actors.every cloud provider is an enemy of uk government. They have gardeners (at best) or lawyers ( most probably), which did their own research.before writing these abominations. At the same time, they want to give all medical datas in the NHS to palantir. This is the apoteosis of incompetence.
All those companies willingly hand over our data when asked. At this point it’s almost a feature
So google, amazon and Microsoft are hostile actors
Obviously not. They’re happy to give MI5 a backdoor into all their systems.
This is the apoteosis of incompetence.
The age old question - malicious or stupid.
Yes end to end encryption is for hostile actors why don’t you send your nuclear launch codes in plain text.
Rules for thee not for me.
Gee why does the capitalist oligopoly fear communication they can’t monitor it’s not like they are doing anything wrong and have anything to fear from little old us
Shit-flinging desperation at the realization that they have failed to contain dissent via internet-based coordination. Elbit and the UK’s protection of property was defeated by persistent disruption thanks to the work by Palestine Action. Unlike previous forms of communication, the empire has had tremendous difficulty wrestling control away because the materiality of the internet is so dispersed, accessible, and impossible to restrict without dire economic and military consequences.
I’m just baffled Labour is trying to die on this hill.
I think Labour is just trying to die.
At this point it feels like they’re being paid to make people vote for Reform who will then make great use of all the surveillance infrastructure that Labour and Tories have put in place
The autonomous murder bots are not complete yet